A Data-Driven Deep Dive | March 2026
Introduction: The Digital Battlefield Has Arrived
The age of the bayonet, the trench, and the infantry charge is over. Today’s wars are fought with lines of code as much as lines of soldiers, with autonomous machines that have never drawn breath deciding who lives and who dies, and with disinformation campaigns that can destabilize democracies faster than any tank column. If you think technology and warfare are topics reserved for generals and Silicon Valley executives, think again. The ripple effects of the new techno-military complex are felt in every smartphone, every hospital network, every power grid, and every household on the planet.
The numbers are staggering. According to the Global Peace Index 2025, the world is now experiencing the highest number of state-based conflicts since the end of World War II — 59 active conflicts simultaneously, with 78 countries entangled in wars beyond their own borders. The global economic cost of violence reached $19.97 trillion in 2024, equivalent to 11.6 percent of the entire world GDP. Military spending alone hit a record high of $2.7 trillion, while investment in peacebuilding collapsed to just 0.52 percent of that total military outlay. The world is, by every measurable metric, arming itself at an unprecedented pace.
But what is fueling this acceleration? Technology. Artificial intelligence, autonomous drones, cyberweapons, hypersonic missiles, satellite surveillance, and quantum computing are transforming conflict so rapidly that legal frameworks, diplomatic institutions, and even the moral philosophy of warfare have been left scrambling to keep up. This blog examines three critical dimensions of this transformation: how technology is actively shaping the current world order of conflict; how ordinary people can harness technology defensively to protect themselves; and the profound double-edged reality of technology as simultaneously humanity’s greatest shield and its most dangerous sword.
“This is the Oppenheimer moment of our generation.” — Austrian Foreign Minister Alexander Schallenberg, Vienna Conference on Autonomous Weapons, 2025
PART I: How Technology Is Influencing the Current World Wars
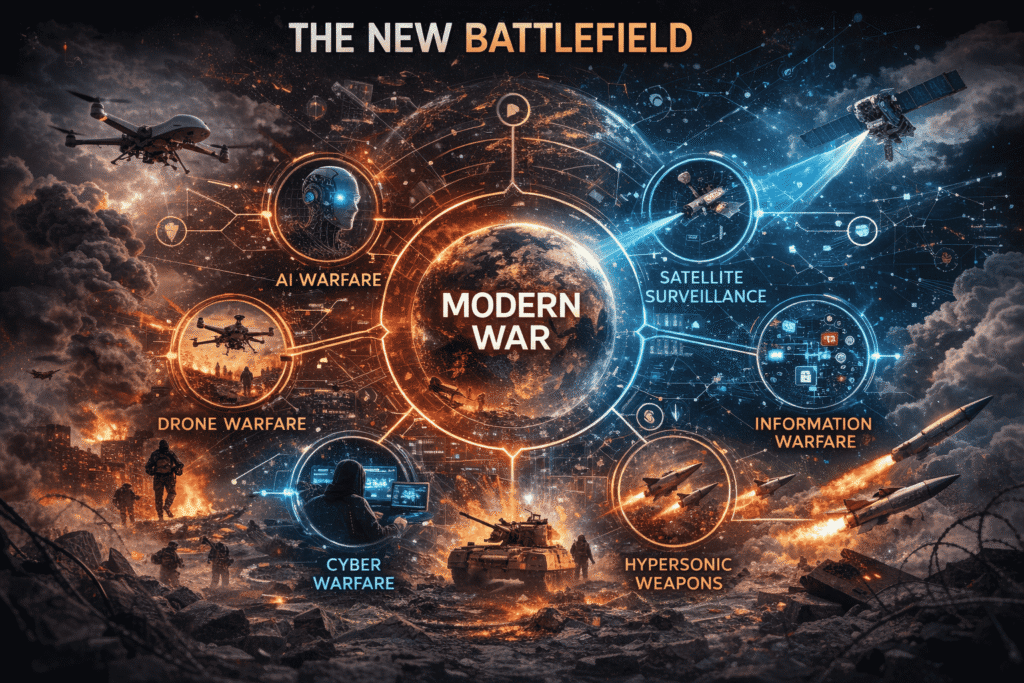
1.1 The Drone Revolution: Flying Robots Take the Front Lines
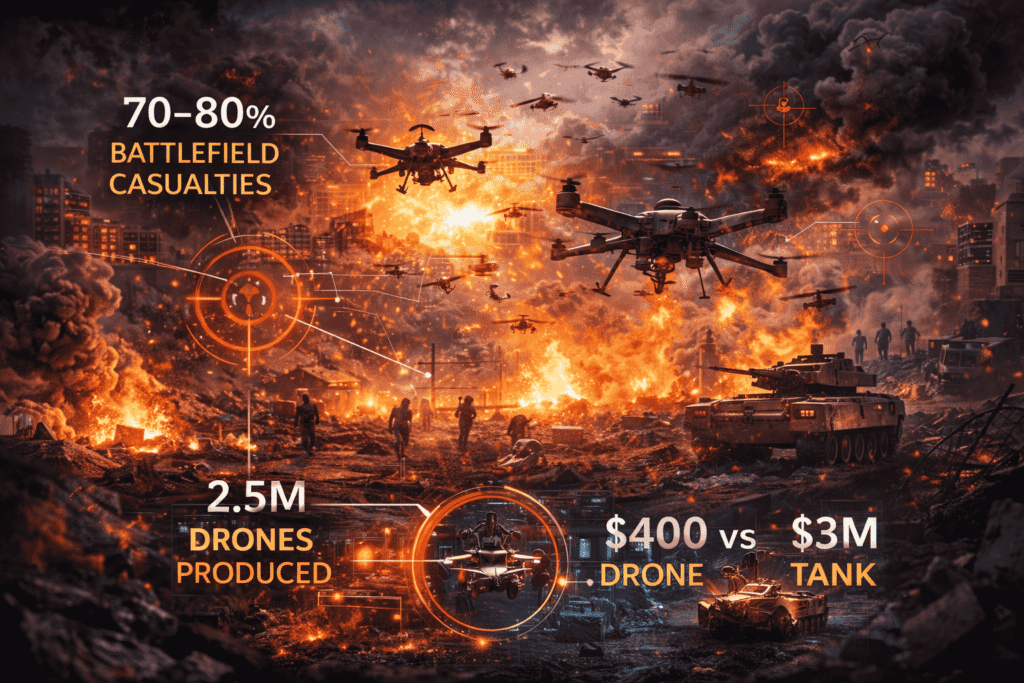
No single technology has transformed modern warfare more visibly or more rapidly than the unmanned aerial vehicle — the drone. From reconnaissance missions to precision strikes, drones have shifted from expensive military assets to cheap, scalable, and terrifyingly ubiquitous weapons of war.
In Ukraine, the statistics are nothing short of extraordinary. By early 2025, drones were accounting for 60 to 70 percent of all damage and destruction inflicted on Russian military equipment, according to the UK-based Royal United Services Institute. A separate report from the U.S. Army War College goes further, stating that drones now cause 70 to 80 percent of all battlefield casualties in the Russia-Ukraine conflict. The sheer scale of production is breathtaking: Ukraine alone is expected to produce more than 2.5 million drones in 2025. Drone attacks by Ukrainian forces have increased by over 127 times since the earliest days of the conflict.
The industry behind this revolution is enormous. The global drone warfare market was valued at $25.2 billion in 2024 and is projected to surge to $41.9 billion by 2030, growing at a compound annual growth rate (CAGR) of 8.8 percent. The number of companies worldwide manufacturing military-grade drones exploded from just 6 in 2022 to over 200 by 2024 — a 3,233 percent increase in just two years.
What makes drones so transformative is their democratization of lethal force. A commercial drone costing a few hundred dollars can be converted into a weapon that destroys a tank worth millions. Ukraine’s experience exemplifies this asymmetric dynamic: a nation outgunned in traditional military hardware has used drone technology to impose catastrophic costs on a numerically and materially superior adversary.
| Metric | Figure |
|---|---|
| Military UAV Market Value (2024) | $15.23 billion |
| Drone Warfare Market Projection (2030) | $41.9 billion |
| Drone manufacturers globally (2024 vs 2022) | 200 vs 6 — a 3,233% increase |
| Drone contribution to Russia-Ukraine casualties | 70–80% |
| Ukraine drone production target (2025) | 2.5 million units |
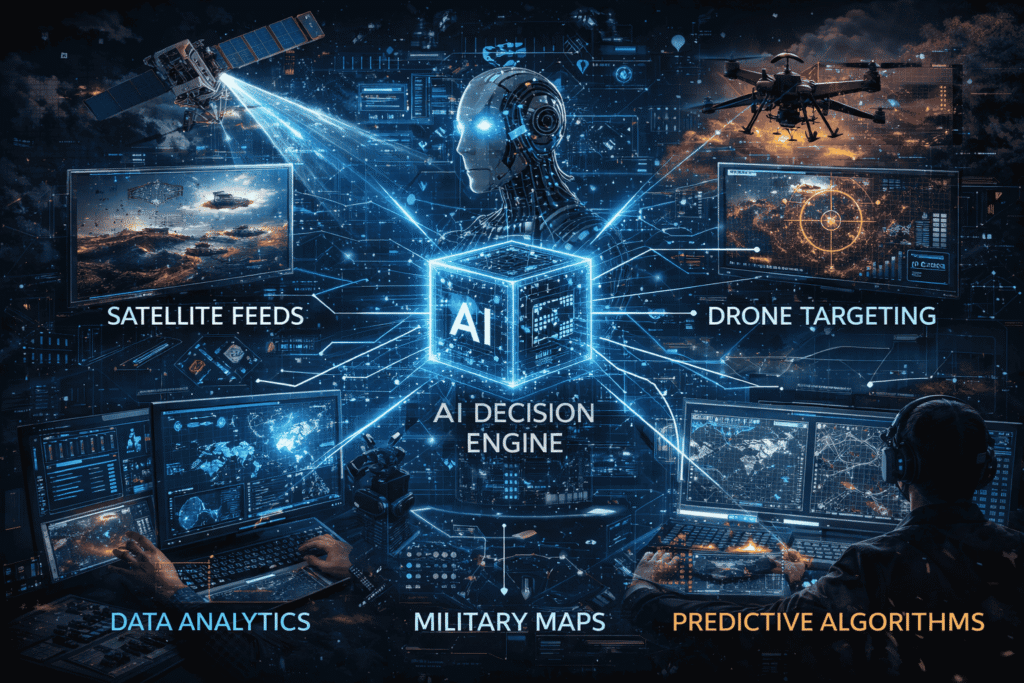
1.2 Artificial Intelligence: The Brain Behind the Machine
If the drone is the sword, then artificial intelligence is the mind wielding it. AI is no longer a future possibility in warfare — it is an active, deployed reality shaping outcomes on today’s battlefields in ways that would have seemed like science fiction a decade ago.
In the Ukraine conflict, AI-based targeting systems can now be added to drones for as little as $25 per unit (approximately 1,000 Ukrainian Hryvnia), according to Lyuba Shipovich, CEO of Dignitas Digital. The impact of this technology is profound: AI-enhanced first-person view (FPV) drone strike accuracy has improved from a baseline of 30 to 50 percent to approximately 80 percent — a near-doubling of precision for one-quarter of a dollar’s worth of software upgrade.
Israel has deployed an AI system called Lavender to process battlefield intelligence data and identify roughly 37,000 Hamas targets during the Gaza conflict. In India’s Operation Sindoor in May 2025, Rafale aircraft paired with SCALP missiles, BrahMos cruise missiles, and Indo-Israeli SkyStriker loitering munitions enabled precision strikes without Indian aircraft entering Pakistani airspace at all — a landmark demonstration of AI-coordinated standoff warfare.
The race to dominate AI in warfare is one of the defining geopolitical competitions of our era. China has committed $150 billion to become the world’s leading AI nation. The U.S. Department of Defense has allocated $1.8 billion for AI and machine learning initiatives in fiscal years 2024 and 2025. The National Security Agency is currently running 170 AI projects, employing 7,000 analysts dedicated to AI integration. Russia, despite a comparatively modest investment of $181 million from 2021 to 2023, is deploying AI-based electronic warfare to jam drone navigation, causing Ukrainian drones to lose satellite lock and fall from the sky.
| Nation / Entity | AI Military Investment |
|---|---|
| China | $150 billion committed |
| United States (DoD FY 2024–25) | $1.8 billion |
| NSA active AI projects | 170 projects / 7,000 analysts |
| Russia (2021–2023) | $181 million |
| Cost to AI-upgrade a single drone | ~$25 per unit |
1.3 Cyberwarfare: The Invisible Front
The fifth domain of warfare — cyberspace — is uniquely dangerous because it knows no borders, respects no treaties, and can strike civilian infrastructure with the ease of typing a command. Cyberattacks have become central to modern geopolitical conflict, and the line between military targets and civilian systems has become vanishingly thin.
The U.S. Department of Defense earmarked $64.1 billion for information technology and cyberspace activities in its fiscal year 2025 budget alone. The electronic warfare market is projected to reach $44.8 billion by 2032, growing at a CAGR of over 4 percent. The global anti-drone market — a direct response to the drone surge — was valued at $1.998 billion in 2024 and is projected to reach $15.578 billion by 2033, a CAGR of 22.79 percent.
State-sponsored cyberattacks on civilian infrastructure are no longer hypothetical. Google’s Threat Intelligence Report highlights that state-sponsored threat actors from China and Iran are actively using advanced AI tools to discover and exploit vulnerabilities in civilian systems — energy grids, hospital networks, financial systems, and water treatment facilities. The attack surface is vast and largely undefended.
Cybercrime is projected to cost the global economy $10.5 trillion annually by 2025, and $23 trillion per year by 2027 according to U.S. Deputy National Security Advisor Anne Neuberger. Security breaches in 2024 were up 75 percent year-over-year. Organizations now face an average of 1,876 cyberattacks per quarter.
The math is brutal: At $10.5 trillion annually, cybercrime would be the world’s third-largest economy — bigger than Japan, bigger than Germany, bigger than every nation on Earth except the United States and China.
1.4 Hypersonics, Space, and the Escalation Ladder
Beyond drones and AI, the technological acceleration in warfare extends into the hypersonic and space domains. Hypersonic missiles — those capable of traveling at Mach 5 (five times the speed of sound) or faster — have been deployed by Russia in Ukraine, tested by China, and are the subject of a furious development race in the United States and India. They are nearly impossible to intercept with existing defense systems and can reach targets in minutes rather than hours.
Space has become an active theater of conflict. Satellite communications enabled Ukraine to maintain battlefield command and control. GPS jamming and spoofing have become standard tools of electronic warfare. The weaponization of space — from anti-satellite missiles to space-based surveillance constellations — represents one of the most destabilizing dimensions of the current arms race.
The long-term consequences are sobering. The number of conflicts resulting in a decisive military victory has collapsed from 49 percent in the 1970s to just 9 percent in the 2010s. Peace agreements as conflict resolution mechanisms have declined from 23 percent to only 4 percent. Wars today are not won and ended — they are managed, sustained, and fed by a constant stream of new technology. As defense budgets grow, peacebuilding investments shrink. The global community is, in a measurable sense, choosing weapons over diplomacy.
PART II: Using Technology to Keep Yourself Safe — A Practical Guide
The militarization of cyberspace is not a distant problem for governments alone. Cyberattacks happen approximately every 3 seconds somewhere in the world — 4,000 attacks daily. In 2025, there are an average of 820,000 IoT attacks per day. The average time for an organization to detect a data breach is 194 days, and the average lifecycle from breach to containment is 292 days — nearly ten months of invisible exposure.
The good news is that technology, the same force enabling these attacks, also provides the tools to protect ordinary people with extraordinary effectiveness. The following is a data-backed practical guide to using technology defensively.

2.1 Understanding the Threat Landscape
Before defense, context. The average cost of a data breach reached $4.44 million in 2025 for organizations. For individuals, the Federal Trade Commission received more than 1.2 million reports of identity theft in 2024 alone. An astonishing 64 percent of Americans have never checked whether their personal data was exposed in a breach. Some 56 percent do not know what steps to take if they discover one.
Phishing attacks — deceptive emails or messages designed to steal credentials — account for more than 80 percent of all reported cybersecurity incidents. Phishing-related breaches are the most expensive, costing an average of $4.88 million per incident. The cost translates to $17,700 lost every single minute globally. AI has supercharged these attacks: phishing attempts surged 1,265 percent over the past year, directly attributed to generative AI tools that can craft perfectly convincing, personalized deception at industrial scale.
2.2 Ten Technology-Backed Steps to Protect Yourself
🔐 Step 1: Enable Multi-Factor Authentication (MFA) on Every Account
MFA is the single most effective security upgrade available to any individual. Organizations using zero-trust approaches — which MFA anchors — saw average breach costs $1.76 million lower than those without, according to IBM. When MFA is enabled, over 99.9 percent of automated account compromise attacks fail, per Microsoft research. Use an authenticator app (Google Authenticator, Microsoft Authenticator, or Authy) rather than SMS-based codes, which are vulnerable to SIM-swapping. Enable it immediately on email, banking, social media, and cloud storage accounts.
🔑 Step 2: Use a Password Manager and Never Reuse Passwords
Credential reuse is one of the leading causes of account compromise. With 94 billion leaked cookies found across dark web markets in 2025, stolen credentials are bought and sold at industrial scale. A password manager generates, stores, and fills unique 16+ character random passwords for every account, eliminating credential reuse entirely. Options like Bitwarden (open source and free), 1Password, or Dashlane use military-grade AES-256 encryption. Never use personal information in a password. Change credentials immediately upon breach notification.
🛡️ Step 3: Keep All Software and Firmware Updated
A staggering 98 percent of web applications are vulnerable to attacks that can result in malware installation or redirection to malicious sites. The overwhelming majority of these vulnerabilities have patches available — the problem is users who delay applying them. Gartner predicted that 45 percent of global organizations would face software supply chain attacks by 2025. Unpatched software is an open door. Enable automatic updates on your operating system, browsers, applications, and router firmware. Set a weekly calendar reminder for devices that do not auto-update.
🌐 Step 4: Use a VPN on Any Public or Untrusted Network
Public Wi-Fi in airports, hotels, and cafes is a hunting ground for man-in-the-middle attacks that intercept unencrypted data. A Virtual Private Network (VPN) encrypts all traffic between your device and the internet. This is critical when accessing banking, email, or any sensitive account on a public network. Choose a reputable, no-log VPN provider. Avoid free VPNs — they frequently monetize user data, the very threat you are trying to avoid. Paid, reputable options include Mullvad, ProtonVPN, and ExpressVPN.
💾 Step 5: Encrypt Your Devices
If your laptop or phone is lost or stolen, full-disk encryption ensures that data on it is unreadable without your credentials. Modern iPhones encrypt by default. Android users should verify encryption is enabled in settings. Windows users should activate BitLocker; macOS users should enable FileVault. For businesses, the average total cost of a breach at a small company was $3.31 million in 2024 — often triggered by a single stolen, unencrypted device. Encryption costs nothing and takes minutes to configure.
🎣 Step 6: Treat Every Unsolicited Communication as a Threat Until Verified
With phishing as the initial attack vector in 16 percent of all data breaches, and AI generating hyper-personalized phishing content indistinguishable from authentic correspondence, the human filter is your most critical defense layer. Verify all unsolicited requests for money, credentials, or personal information through a separate, known channel. If your bank emails you, call the number on the back of your card — not a number in the email. The FBI warns that deepfake audio calls impersonating executives are now being used to authorize fraudulent wire transfers. Zero-trust skepticism is not paranoia; it is survival hygiene.
🔍 Step 7: Monitor Your Digital Footprint Proactively
Services like HaveIBeenPwned.com allow you to check within seconds whether your email address appears in any known data breach. Set up Google Alerts for your full name. Monitor your credit reports through all three major bureaus — Equifax, Experian, and TransUnion — which provide free annual reports. Consider a credit freeze if you have been a breach victim. In 2024, over 560 million Ticketmaster customers had their data stolen in a single breach. Proactive monitoring turns a 194-day average detection window into immediate awareness.
🏠 Step 8: Secure Your Smart Home and IoT Devices
The average home now contains dozens of internet-connected devices — cameras, thermostats, door locks, televisions, and appliances — each a potential entry point. In 2025, IoT attacks average 820,000 per day globally. Default manufacturer passwords on routers and smart devices are the most common entry point for attackers. Change all default passwords immediately upon setup. Place IoT devices on a separate guest Wi-Fi network, isolated from your main computers and phones. Update router firmware at least quarterly.
💽 Step 9: Follow the 3-2-1 Backup Rule — Religiously
Ransomware attacks — where criminals encrypt your files and demand payment — are the fastest-growing cyber threat category. Ransomware recovery costs averaged $3.58 million for organizations in 2025. The antidote is disciplined backup practice: maintain 3 copies of critical data, on 2 different types of media, with 1 copy stored offline or off-site. For individuals: a local external drive, a cloud backup service, and a second physical copy elsewhere. With this in place, a ransomware attack becomes an inconvenience. Without it, it becomes a catastrophe.
📚 Step 10: Invest in Continuous Cybersecurity Education
The global cybersecurity workforce is short 4.8 million professionals in 2025. Organizations that invest in security awareness training see dramatically better outcomes: AI-driven personalized security training is projected to reduce employee-driven incidents by 40 percent by 2026. For individuals, free resources include the CISA (Cybersecurity and Infrastructure Security Agency) website, Google’s free Phishing Quiz, and the SANS Internet Stormcast daily podcast. The cost of learning is zero. The cost of ignorance can be your life savings, your medical records, or your identity. Treat cybersecurity education like an annual health check-up: mandatory, routine, and non-negotiable.
Security AI reduced breach costs by 34% in 2025, saving organizations an average of $1.9 million per incident (IBM). The same AI-powered tools — threat monitoring services, password managers, identity protection platforms — are available to individuals for a few dollars a month or even free.
PART III: Technology as Curse and Blessing — The Dual-Use Dilemma
3.1 The Blessing: Technology as the Great Equalizer and Lifesaver
Before cataloging the dangers, honesty demands acknowledging the extraordinary positive power technology has brought to the human experience — including in the context of conflict and security.
Medical technology has dramatically reduced combat fatality rates. The case fatality rate for battlefield injuries today is a fraction of World War II levels, thanks to telemedicine, AI-assisted triage, advanced prosthetics, and rapid evacuation systems enabled by GPS and real-time communication. Satellite imagery and drone surveillance have enabled humanitarian organizations to identify and respond to crises faster than ever, potentially saving hundreds of thousands of lives in disaster zones from Syria to the Sahel.
Communication technology has given voice to the oppressed. Civilians in conflict zones document war crimes in real time on smartphones. Citizen journalists in Ukraine, Gaza, and Sudan have transmitted footage that has shaped international public opinion and generated accountability pressure in ways no traditional media infrastructure could achieve. The speed and reach of digital communication is a force for transparency that authoritarian regimes increasingly struggle to suppress — even as they desperately try.
Defensive technology is growing exponentially effective. Security AI reduced breach costs by an average of $1.9 million per incident in 2025, a 34 percent reduction. AI-powered anomaly detection systems identify network intrusions in hours rather than months. Automated threat intelligence platforms ingest billions of indicators of compromise daily, something no human team could match. Gartner projects that by 2026, over 60 percent of threat detection, investigation, and response capabilities will leverage AI-driven exposure management data — up from less than 5 percent today.
The global cybersecurity market is projected to reach $200 billion by 2028. Cybersecurity Ventures forecasts global spending on security products and services hitting $522 billion annually by 2026. This represents millions of jobs, significant innovation, and economic growth in a sector whose fundamental mission is protection rather than destruction.
The Evolution of Modern Warfare: How Technology is Transforming the Rules of War3.2 The Curse: Autonomous Violence, Disinformation, and the Erosion of Control
Yet for every defensive application, every humanitarian use case, and every economic opportunity, technology simultaneously opens equally powerful vectors for harm — and the trajectory of those vectors is deeply troubling.
When Machines Decide Who Dies
The most chilling development in military technology is the progression toward autonomous lethal systems — weapons that can identify, select, and kill targets without meaningful human involvement. The ethical stakes are unlike anything in the history of warfare. Austrian Foreign Minister Schallenberg’s Oppenheimer comparison is not hyperbole. Like nuclear weapons in the 20th century, autonomous AI weapons threaten to fundamentally and irreversibly alter the nature of human conflict.
The trajectory is visible in current data. AI-enabled drones already reduce human decision-making in strike sequences. Ukraine’s long-range drones carry AI capable of autonomously identifying terrain features and military targets. Russia is developing counter-systems that operate at machine speed. When AI systems engage each other in conflict, decisions happen at speeds humans cannot match — and that speed compresses moral judgment completely out of the operational loop. The so-called black box problem means that even the developers of these systems often cannot fully explain why a particular kill decision was made.
Legal frameworks are hopelessly behind. The Convention on Certain Conventional Weapons’ Group of Governmental Experts held discussions in 2024 on lethal autonomous weapon systems — yet no binding legal framework has emerged. Nearly every major military power is deploying these systems faster than any international governance structure can regulate them.
Disinformation as a Weapon of Mass Disruption
Cognitive warfare — the deliberate manipulation of populations’ beliefs and perceptions through technology — is now explicitly recognized by China’s People’s Liberation Army as co-equal to air, land, and sea domains. Russia’s deployment of social media manipulation, deepfake video, and AI-generated propaganda has been documented in at least 27 countries. The tools are cheap, scalable, and devastatingly effective.
The deepfake threat deserves special attention. AI-generated audio and video are now indistinguishable from reality at casual inspection. Synthetic identities now account for over 80 percent of new account fraud (Experian). 47 percent of organizations have already experienced deepfake-based attacks. AI-enabled phishing surged 1,265 percent in one year — a rate of expansion that overwhelms conventional defensive response systems.
The consequences extend far beyond individual fraud. When citizens cannot reliably distinguish real video from fabricated video of their president, their military, or their neighbors, the foundational social trust that holds democracies together begins to corrode. Disinformation campaigns do not need to convince people of falsehoods — they only need to create sufficient doubt about truth itself. Technology has made lying at industrial scale effortless, cheap, and largely consequence-free.
The Digital Divide and Asymmetric Danger
Technology does not distribute its benefits or burdens equally. Wealthy nations with access to cutting-edge AI and drone technology enjoy massive asymmetric advantages over populations that lack these tools. But asymmetry also runs in dangerous directions: non-state actors — terrorist organizations, drug cartels, paramilitary groups — now access commercial drones weaponizable for a few hundred dollars. In fragile states across the Sahel, sub-Saharan Africa, and South Asia, drone technology is spreading to rebel groups with no accountability, no chain of command, and no compliance with international humanitarian law.
The data paints a stark picture of where this leads. The Global Peace Index 2025 identifies South Sudan, Ethiopia, Syria, and the Democratic Republic of the Congo as high-risk escalation zones precisely because cheap technology is lowering the threshold for organized violence. The global average military expenditure as a share of GDP rose for the ninth consecutive year in 2024. Simultaneously, the global number of nuclear warheads — after decades of reduction — is rising again for the first time since the Cold War, with approximately 12,100 warheads currently held by nine nations.
| Escalation Indicator | Data |
|---|---|
| Nuclear warheads globally (2025) | ~12,100 across 9 nations |
| Consecutive years of rising military spending | 9 years |
| Active conflicts simultaneously (2025) | 59 |
| Cost of violence as % of global GDP | 11.6% ($19.97 trillion) |
| Conflicts ending in decisive victory (2010s) | Only 9% (vs 49% in the 1970s) |
3.3 The Balance Sheet: A Framework for Clarity
The curse-versus-blessing debate around technology is ultimately not a binary. Technology is a multiplier — it amplifies the intentions of those who wield it. When wielded by democratic institutions, medical researchers, cybersecurity defenders, and humanitarian organizations, it saves lives, protects rights, and expands human freedom. When wielded by authoritarian states, criminal networks, and terrorist organizations, it scales destruction, erodes truth, and concentrates violence in previously unimaginable ways.
The fundamental challenge of our era is governance. The question is not whether to have the technology — that ship has sailed. The question is whether humanity can build the international agreements, domestic legal frameworks, ethical guidelines, and individual habits of mind to govern technology’s most dangerous applications before those applications govern us.
The facts argue for urgency. In a world where a $25 AI upgrade can double the legality of a drone, where cyber crime is on track to be the world’s third-largest economy at $23 trillion by 2027, where 59 conflicts rage simultaneously and peacebuilding receives less than 1 percent of what militaries spend, the stakes of technological governance are existential.
Learn how to grow your real estate brokering business in 2026 using Meta AdsConclusion: We Are All on the Digital Battlefield
You do not have to be a soldier to be a casualty of technological warfare. Every unpatched router is a potential entry point for a state-sponsored hacker. Every reused password is a credential waiting to be sold on a dark web marketplace. Every deepfake video you share without verification may be a foreign intelligence operation designed to fracture your community. And every dollar in global military AI spending that outpaces arms control negotiation brings the world one step closer to a conflict no human chose and no algorithm can undo.
But you also do not have to be helpless. The same technology that arms adversaries also arms defenders. A $0 authenticator app blocks 99.9 percent of automated account attacks. A $10-per-month VPN encrypts your internet traffic from surveillance and interception. A free backup to an external drive protects you from ransomware. Education — available freely online at CISA, SANS, and dozens of reputable institutions — closes the knowledge gap between you and the threat actors hunting you.
The deeper lesson of this technological moment is one about human choice. Technology does not have values. It does not care whether it protects a child in a conflict zone or kills one. It does not care whether it exposes corruption or invents it. It does not care whether it secures your bank account or empties it. Those outcomes are determined entirely by the choices of human beings — from the engineers who build it, to the governments that deploy it, to the individuals who use it every day.
The global economic cost of violence in 2024 was $19.97 trillion. The number of people in active conflict is in the tens of millions. The number of cyberattack victims is in the billions. These are not inevitable numbers. They are the cumulative result of human decisions about how to build, deploy, govern, and resist technology. Which means they are numbers that human decisions can change.
The battlefield is everywhere now. The only question is which side of the technology you choose to stand on.